Project Policy Validation with OPA and ansible-policy
By Luca Berton · Published 2024-01-01 · Category: installation
A comprehensive guide to setting up and using the Ansible Policy tool for managing policies in your Ansible projects and create effective Rolebook.
Introduction
There's a new Ansible feature in town, and I'm thrilled to announce the Ansible Policy utility, which can directly interact with the Open Policy Agent (OPA). If you're familiar with Kubernetes, you might already know OPA's popularity for specifying rules and validating projects against them.
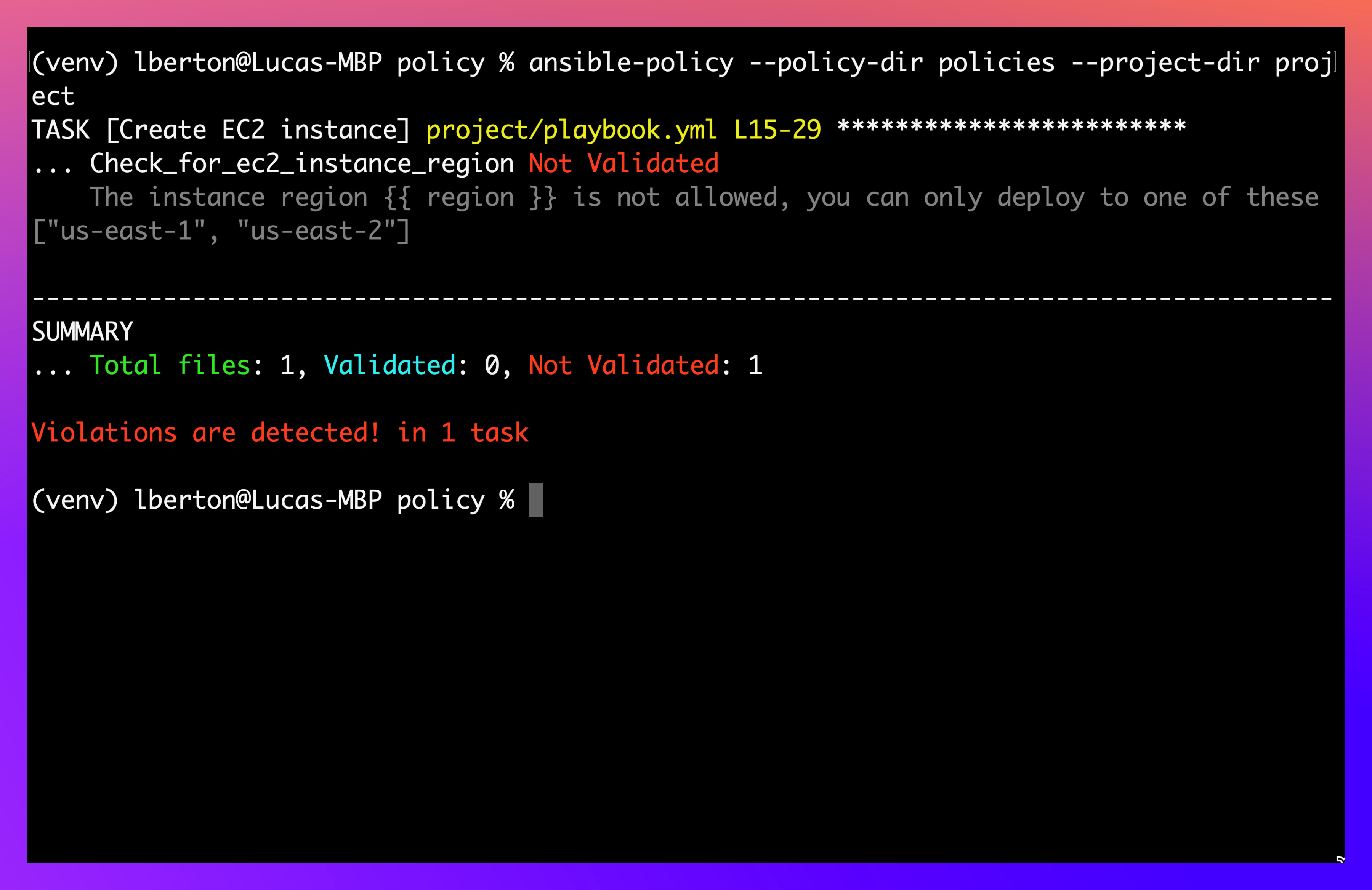
This utility is particularly beneficial for organizations that need to ensure their projects comply with specific policies. For instance, in this example, I'll validate my playbook against a policy that restricts AWS EC2 machine allocation to the US East 1 and US East 2 regions. As you'll see, my playbook isn't compliant, as specified on lines 15 and 29, because it attempts to allocate machines in different regions.
By flagging non-compliance, we prevent the execution of configurations that don't meet our standards. So, why haven't you heard about Ansible Policy? Because it's a new prototype implementation that allows you to define and set OPA rules within your application using the Ansible Policy utility.
Architectural Diagram
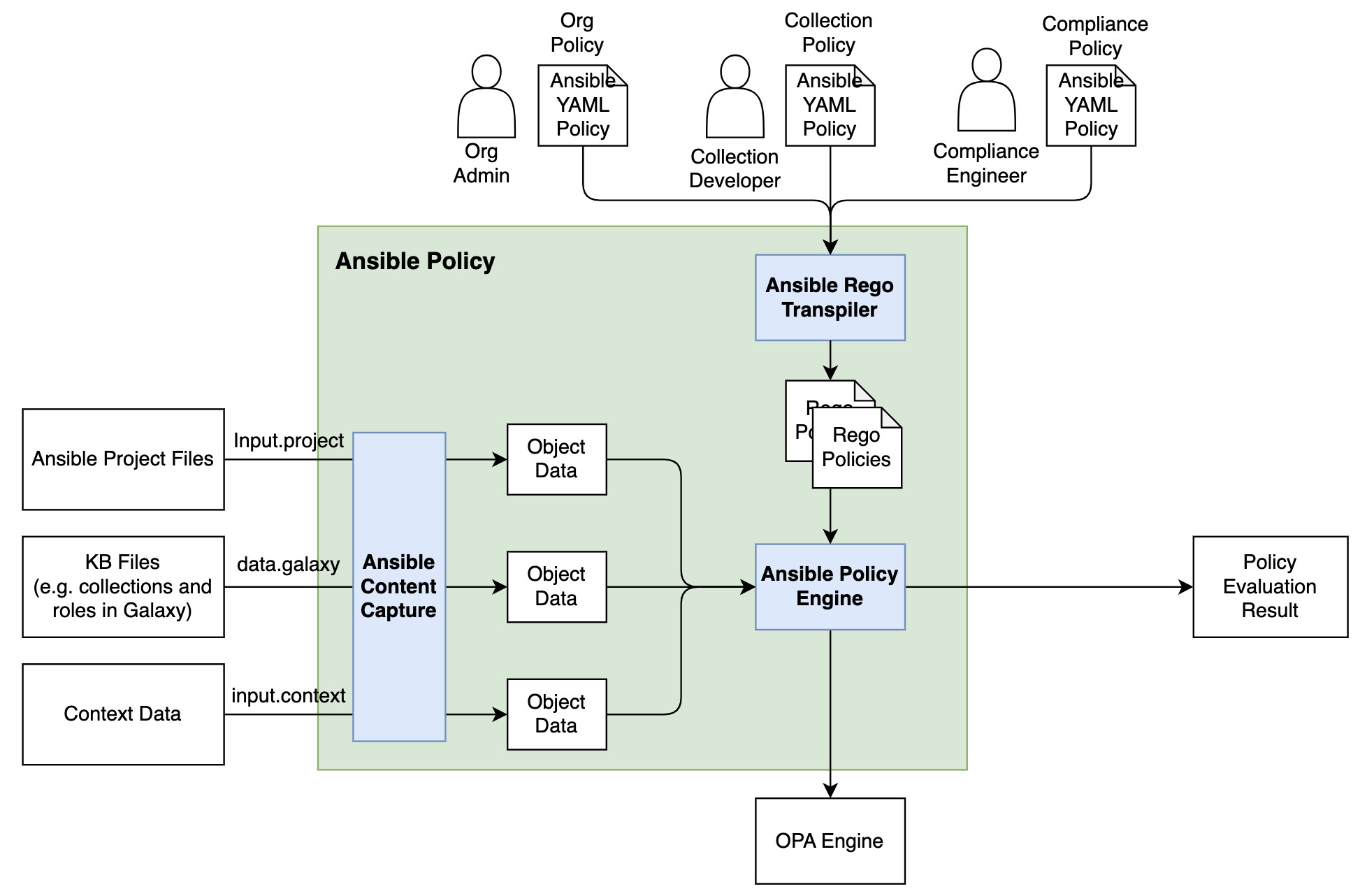
Here's an architectural diagram illustrating the interaction between the Ansible Policy engine, the Ansible repository, the rules, and how you can validate your project. Everything is integrated, relying on the API command by the Ansible Policy command line utility, which ultimately provides a validated or not validated result.
Installation Guide
To install the Ansible Policy command, follow these steps: Set Up a Python Virtual Environment: Since this is an experimental feature, it's better to avoid cluttering your system with additional libraries.
python3 -m venv ansible-policy-env
source ansible-policy-env/bin/activate
pip install -e .
This command will download all necessary libraries and install them. Dependency Management: You might encounter a few roadblocks if all dependencies aren't satisfied. First, deactivate and reactivate the virtual environment.
deactivate
source ansible-policy-env/bin/activate
pip install ansible
brew install opa
Now, the ansible-policy command should be available. If you invoke it without parameters, ensure to use --help or the correct options to avoid exceptions.
Using Ansible Policy
With Ansible Policy installed, you can specify configurations like ansible.config, the target directory, and the policy directory. Here’s an example configuration file and a non-validated playbook specifying packages below the region in my AWS instance:
# policybook.yml
---
- name: Check for ec2_instance region
hosts: localhost
vars:
allowed_instance_regions:
- us-east-1
- us-east-2
policies:
- name: Check for ec2_instance region
target: task
condition: input["amazon.aws.ec2_instance"].region not in allowed_instance_regions
actions:
- deny:
msg: The instance region {{ input["amazon.aws.ec2_instance"].region }} is not allowed, you can only deploy to one of these {{ allowed_instance_regions }}
tags:
- compliance
# playbook.yml
---
- name: Provision EC2 instance
hosts: localhost
gather_facts: false
become: true
vars:
region: "us-west-1"
instance_type: "t2.micro"
ami_id: "your_ami_id"
key_name: "your_key_name"
security_group: "your_security_group_id"
subnet_id: "your_subnet_id"
tasks:
- name: Create EC2 instance
amazon.aws.ec2_instance:
region: "{{ region }}"
key_name: "{{ key_name }}"
instance_type: "{{ instance_type }}"
image_id: "{{ ami_id }}"
security_group: "{{ security_group }}"
subnet_id: "{{ subnet_id }}"
assign_public_ip: true
wait: yes
count: 1
instance_tags:
Name: "MySQLInstance"
register: ec2
output
(venv) lberton@Lucas-MBP policy % ansible-policy --policy-dir policies --project-dir project
TASK [Create EC2 instance] project/playbook.yml L15-29 ************************
... Check_for_ec2_instance_region Not Validated
The instance region {{ region }} is not allowed, you can only deploy to one of these ["us-east-1", "us-east-2"]
-----------------------------------------------------------------------------------------
SUMMARY
... Total files: 1, Validated: 0, Not Validated: 1
Violations are detected! in 1 task
(venv) lberton@Lucas-MBP policy %
Executing the policy validation against this playbook would result in an error if the region isn't compliant.
ansible-policy --policy-dir policies --project-dir projectConclusion
The Ansible Policy utility is a powerful tool for enforcing compliance and ensuring your configurations meet organizational standards. By integrating with OPA, it provides flexible, fine-grained control over your automation scripts. I can't wait to hear your automation stories and use cases with the policy book.
Let's automate more!
For more information, check out: • Open Policy Agent • Ansible Policy GitHub Repository
Keep exploring and happy automating!
Bye and happy automating!
See also: Ansible Troubleshooting: Resolving community.aws.ec2_instance Issues
Related Articles
• how Ansible become works under the hood • EC2 provisioning with AnsibleCategory: installation
Watch the video: Project Policy Validation with OPA and ansible-policy — Video Tutorial